Weak or broken authentication is acknowledged by the OWASP as easily exploitable by hackers with extreme damage potential. Users need to be authenticated when they are trying to access an application or a service in a reliable, secure (and convenient) manner but this is not always practiced. 81% of data […]
Yearly Archives: 2020
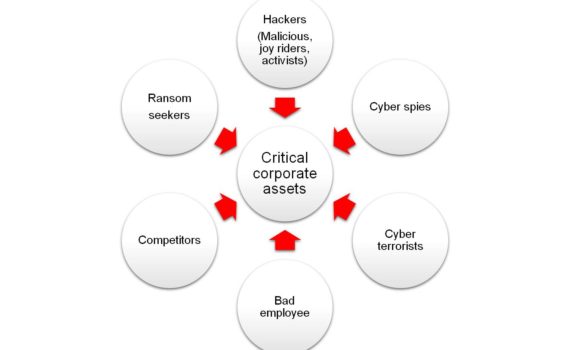
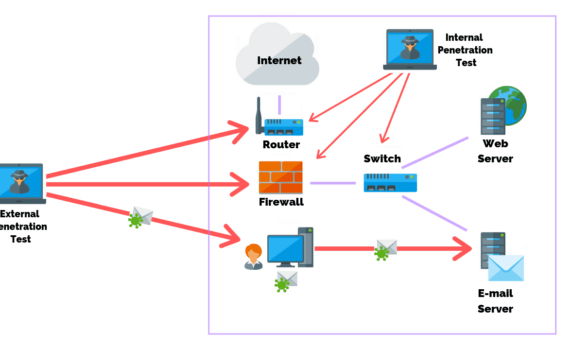
Businesses need to scan the external available infrastructure and applications to protect against external threats. They also need to scan internally to protect against insider threat and compromised individuals. Pen testing should be conducted regularly, from monthly, to possibly quarterly. Because of the constantly evolving threat universe, once a month […]
We are trying hard to make it really tough for hackers to break into you network but what happens when they do? In the OWASP top 10, #3 deals with preventing sensitive data from being exposed in the event that a successful attack is made. This in turn can help […]
Multi-factor authentication is an authentication method in which a computer user is granted access only after successfully presenting two or more pieces of evidence to an authentication mechanism: The 3 factors are typically: knowledge (what you know), possession (what you have, like a phone or access to an email account), […]
A Hacking Simulation Penetration testing is a hacking simulation conducted with the purpose to create an event as close as possible to a real attack to test an environment’s cybersecurity posture, and eventually identify solutions to secure it, limiting exposure to threats and attacks. Pen-testing is a systematic process that […]
Businesses need to regularly scan the external available infrastructure and applications to protect against external threats. They also need to scan internally to protect against insider threat and compromised individuals. The worst situation is to have an exploitable vulnerability within your infrastructure, application or employees, that you are not aware […]